Blog
-

Taking the Risk out of Customer Identity Migration
When it comes to Customer Identity integration, Migration is an almost inevitable part of the journey, and one that can be a challenging and risky prospect if not approached in the right way. In this article, I’ll be discussing what you’ll need to consider in order to make your transition as smooth as possible.
-

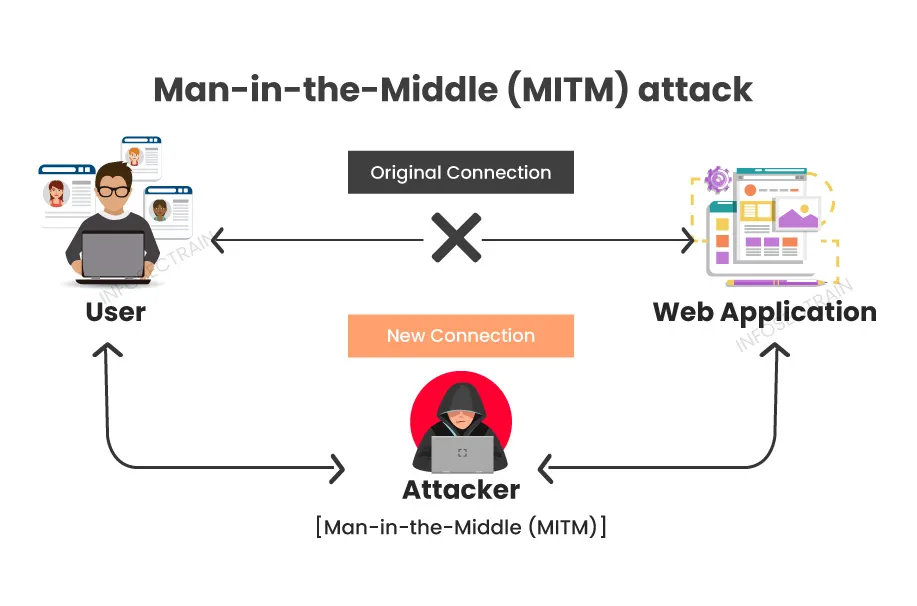
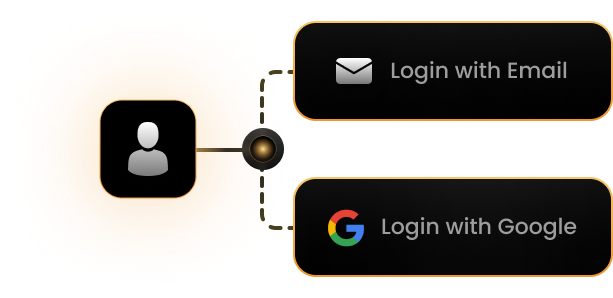
Why Account Linking Should Be Pivotal in your CIAM SSO
Account linking isn’t just a technical feature, it’s a strategic capability you’ll almost certainly want to employ. The ability to recognize and unify customer identities not only offers a competitive advantage, but in an SSO context is a necessity to unlocking the full potential of the user experience, data integrity, personalization, security, and compliance.
-

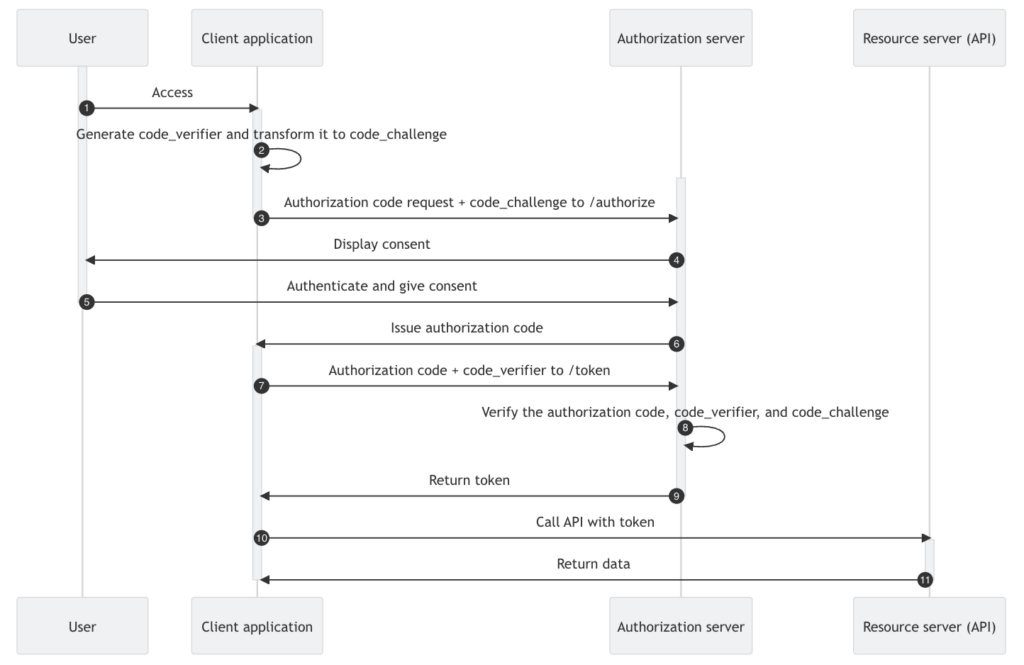
Vibe Coding Authentication via Authorization Code Flow
Developers frequently inquire about integrating CIAM Authentication via a standard like OIDC. Using Authorization Code Flow as the recommended best practice, this article explores using Vibe coding with Copilot AI to addresses the practical steps required in a Next.js application, leveraging NextAuth.js and Keycloak as part of the solution design.
-

Anatomy of a Password
Password authentication remains a cornerstone of Customer Identity and Access Management (CIAM) systems, but to be effective, it must be secure. Passwords must never be stored in plain text, proper encryption, hashing and salting techniques must be employed, and regular monitoring with periodic auditing is essential to keeping password data secure.
-

Architecting a CIAM Solution
CIAM architecture includes several core components all working together to deliver a seamless and secure experience for users. By adopting best practices in security, privacy, and user experience, B2C and B2B SaaS developers can build trust with their customers while ensuring compliance with evolving data protection regulations.
-

An API-First Approach to CIAM
Customer Identity and Access Management (CIAM) involves addressing a variety of scenarios in an increasingly complex digital landscape. Adopting an API-first approach offers several advantages, particularly when it comes to integrating with your existing management systems and doing so in the context of Continuous Integration (CI) and Continuous Deployment (CD).